2017’s first “What is Xojo?” webinar was well received and there were lots of questions. Rather than include the questions in the video, I’ve included a…
Comments closedXojo Programming Blog Posts
We were really pleased to get all the great feedback our Livin’ La Vida Linux blog post. People sure love Linux! A few people asked about…
Comments closedIn desktop apps, you can use Xojo.Core.Locale to get the user’s locale for formatting dates and numbers. However, in a web app this value returns the locale used by the web server rather than the locale of the current user session.
To display dates formatted in the locale of the user session, you need to get the LanguageCode from WebSession and use that to create a locale that you can then use to display the date.
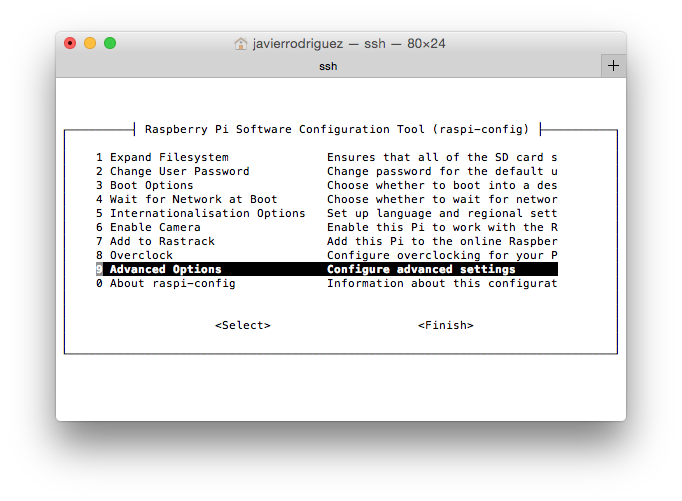
Comments closedYou already know, you can use Xojo to create practically any kind of application; from apps used by corporations, Universities and even Government agencies around the world, to apps used by photographers, designers and, of course, developers; and even those small utilities that makes our lives a bit easier.
In fact, a lot of these little utilities are what are known as Wrappers. That is, a nice user interface that simplifies and makes more user friendly a feature that is already available in the native operating system; often, in the form of one or more combined commands that need to be typed from the Command Line prompt.
You can watch the video (in Spanish, with English subtitles) as you read and work through this example.
Comments closedDo you recall when your most indispensable app was last updated?

As you may already know, 2016 was Xojo’s 20 Anniversary. Sitting down to write this post, I can’t help but think back to 20 years ago and starting what has now become Xojo. Most of the developer tools that were around when we started either no longer exist or are no longer published by the people who had the original vision to create them in the first place. In that respect, we are members of a very exclusive club. I’m also pleasantly surprised at how many users from way back then are actively using Xojo today. I take great pride in the fact that we have created something that has that kind of staying power.
Comments closedIDE Scripts to the rescue! With a simple script (less than 10 lines), whenever you have quoted text to paste into the IDE, just select your script from the File > IDE Scripts menu instead.
Comments closedXDC 2016 was in Houston in October 2016, developers from all over the world gathered for three days of nonstop Xojo excitement. Did you know that planning for the next XDC started the following week? After surveying many people and listening to the comments we received from attendees, we have decided that springtime is generally preferred, so the next XDC will take place in late-April of 2018! Stay tuned for more details….
Comments closedDo you live the Linux life? If so, you might want to try Xojo on Linux to see how easy it is to make your own…
Comments closedXojo is a superb choice for developing and deploying apps for Raspberry Pi. After all, Xojo not only simplifies making the User Interface of your apps via drag and drop, it’s an object-oriented and event oriented programming language that builds native Linux apps based on the ARM processor architecture for the Raspberry Pi (among other platforms).
Comments closed